Overview of the Cisco ASA
There are tons of differences between Cisco ASA platforms and software licenses. This lab will discuss and demonstrate how to identify Cisco Adaptive Security Appliance hardware and license information.
- Core Knowledge
- Lab Topology
- Initial Configs
- Lab Objectives
- Lab Instruction
Core Knowledge and Real World Scenarios
Welcome to the wonderful world of Cisco Adaptive Security Appliances. The Cisco ASA is an extremely popular firewall used by millions of companies around the globe to secure their network from unauthorized access and a broad range of sophisticated attacks. Coupled with the SSM-AIP (Advanced Instruction Prevention module); the Cisco ASA can not only filter traffic based on access-list but can also inspect application layer traffic and enforce security policies based on signature attacks such as SQL Injections, Worms, Mal-ware and even certain types of SPAM.
So lets start with the 20,000 foot view of the Cisco ASA. In a nut shell, the ASA is a deep packet inspection security device used to protect your network(s) against unauthorized access. The Cisco ASA has many functions, some of which include enforcing access control lists, randomizing source port numbers sequence numbers while enforcing protocol compliance.
For example, a PC on the inside of your companies network wants to communicate to Google.com; First your PC sends a TCP SYN packet with a random source port number and a destination port number of 80 towards Google web server IP address. The firewall receives this frame as it is in the transit path between the PC and the Server and it inspects this packet to ensure that it meets compliance of the HTTP protocol. Basically ensuring that the HTTP packet is really an HTTP packet. Once approved by the inspection policy, it is than routed out the egress interface with a new source port number which becomes the destination port number for Google return traffic along with a randomized sequence number. The firewall also places a dynamic entry into the state table which is basically an ACL entry permitting return traffic from Google to the PC that requested the traffic.
The Cisco ASA has a very similar command line interface to Cisco Routers and Switches however it does slightly differ. For example, the show ip interface brief command on a router is reversed on an ASA as show interface ip brief. While working with the ASA’s you will notice several differences which will initially frustrate you if you’re new to Cisco firewalls, however you will also notice several things that you can do on an ASA that you cannot do on Cisco IOS from a command line perspective.
The Cisco ASA evolved from the Cisco PIX which was a platform that Cisco acquired from Network Translation Inc. in 1995. The PIX; originally developed by John Mayes was designed to alleviate the exhaustion of the IPv4 address space by hiding multiple inside host behind a single IP Address similar to how legacy PBX systems handled internal extensions. Thus the concept of Dynamic NAT was born. The original PIX operating system was based on Finesse OS which executed a UNIX Kernel. The Cisco PIX however, in all its former glory was announced End of Life on January 28th, 2008.
If you want to read more on the history of the PIX (Private Internet eXchange) Firewall check out: History of the PIX Firewall
Once upon a time the Cisco PIX and Cisco ASA co-existed peacefully, even ran very similar operating systems starting with 7.0. While the two operating systems had a similar command line interface but functionally at its core, they could not be further apart.
The Cisco ASA’s were announced in 2005 and were a huge success almost instantly. Those who were familiar with the Cisco PIX had a platform to migrate to without major changes in the configuration or management interface. Cisco ASA’s are based on the x86 architecture just like its predecessors however the ASA’s now utilized Compact Flash Cards and supported several new features that of which the Cisco PIX could not such as SSL VPN technology.
The licensing structure of the Cisco ASA is very similar to the PIX in that the licensed features are activated via an “Activation-Key” which is a 4 or 5 tuple key. In a nut shell this key is an MD5 or SHA1 hash broken out into 4 or 5 words using the following structure:
Activation-Key: 0x00000000 0x00000000 0x00000000 0x00000000 0x00000000
This activation key dictates which features the device can utilize such as how many remote SSL VPN clients are licensed to connect, inside hosts, failover, cryptographic features and more.
There are several different models of the Cisco ASA with each model providing different performance specs. While the performance may differ, the operating system that they run is exactly the same. So if you’ve ever worked on a Cisco 5510, you would not notice a difference between the 5510 and the 5585-X from a command line perspective. If you wish to view the difference between the Cisco ASA’s you should check out Cisco.com – Compare Cisco ASA Models
As a network security analyst it is extremely hard not to come across Cisco ASA’s in the enterprise network. Cisco ASA’s are commonly used as SSL VPN remote access concentrators, LAN2LAN termination gateways and in many cases internet edge firewalls.
While the Cisco ASA has tons of advanced security features, this workbook will focus on the general basic of everyday ASA management. While the Cisco ASA may have a similar CLI compared to Cisco IOS, knowing the subtle differences will make your life that much easier.
Familiarize yourself with the following command(s);
| Command | Description |
|---|---|
| show version | This command is is similar to its Cisco IOS Counterpart, it displays all information regarding software version, asdm version, up time, interface mac addresses and licensing information. |
| show cpu | This command when executed in privileged mode displays the CPU percentage utilization for the past 5 seconds, 1 minute and 5 minutes. |
| show memory | This command when executed in privileged mode displays the current memory utilization statistics. |
Lab Logical Topology
The following logical topology is used in all labs found through out Section 9 of the CCNA Security Workbook;
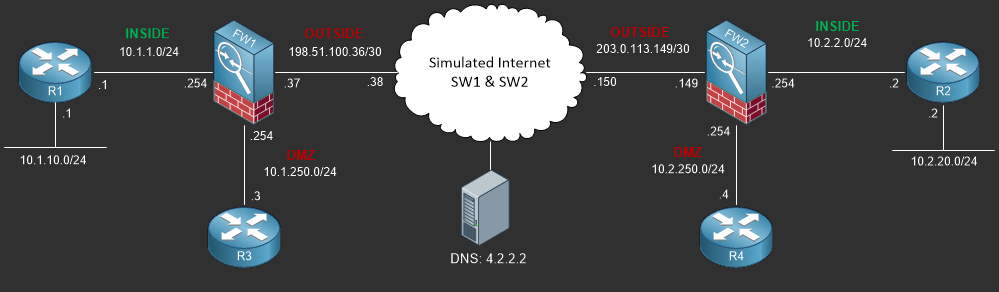
To view the physical cabling topology please visit the Topology page.
Lab Device Initial Configurations
There are no initial configurations required for this Lab.
Before you Start
This lab requires that you have access to a Cisco ASA. You can complete this lab using a virtual Cisco ASA within GNS3 or you can reserve lab time on the Stub Lab to have free access to Cisco ASA 5505 Series Firewalls which can be used to complete this lab.
Lab Objectives
In this lab you will complete the following objectives.
- Determine which version of Cisco ASA Software is currently running on your firewall and what features your firewall is licensed for.
- Users have been complaining about performance when accessing the internet. Determine the memory and processor utilization on your firewall.
One More Thing…
It is recommended that you attempt to complete these lab objectives the first time without looking at the Lab Instruction section.
If you are a student preparing for the Cisco CCNA Security Certification Exam than you are more likely to remember how to complete these objectives if you attempt to complete them the first time on your own
with the use of the core knowledge section found in this lab. You should only resort to the Lab Instruction section to verify your work.
Lab Instruction
Objective 1. – Determine which version of Cisco ASA Software is currently running on your firewall and what features your firewall is licensed for.
This objective can be completed using the show version as demonstrated below;
FW1# show version
Cisco Adaptive Security Appliance Software Version 9.1(1)
Device Manager Version 7.1(1)
Compiled on Wed 28-Nov-12 10:38 by builders
System image file is "disk0:/asa911-k8.bin"
Config file at boot was "startup-config"
FW1 up 47 mins 25 secs
Hardware: ASA5505, 512 MB RAM, CPU Geode 500 MHz,
Internal ATA Compact Flash, 128MB
BIOS Flash M50FW080 @ 0xfff00000, 1024KB
Encryption hardware device : Cisco ASA-5505 on-board accelerator (revision 0x0)
Boot microcode : CN1000-MC-BOOT-2.00
SSL/IKE microcode : CNLite-MC-SSLm-PLUS-2.03
IPSec microcode : CNlite-MC-IPSECm-MAIN-2.08
Number of accelerators: 1
0: Int: Internal-Data0/0 : address is 0025.8454.ce0f, irq 11
1: Ext: Ethernet0/0 : address is 0025.8454.ce07, irq 255
2: Ext: Ethernet0/1 : address is 0025.8454.ce08, irq 255
3: Ext: Ethernet0/2 : address is 0025.8454.ce09, irq 255
4: Ext: Ethernet0/3 : address is 0025.8454.ce0a, irq 255
5: Ext: Ethernet0/4 : address is 0025.8454.ce0b, irq 255
6: Ext: Ethernet0/5 : address is 0025.8454.ce0c, irq 255
7: Ext: Ethernet0/6 : address is 0025.8454.ce0d, irq 255
8: Ext: Ethernet0/7 : address is 0025.8454.ce0e, irq 255
9: Int: Internal-Data0/1 : address is 0000.0003.0002, irq 255
10: Int: Not used : irq 255
11: Int: Not used : irq 255
Licensed features for this platform:
Maximum Physical Interfaces : 8 perpetual
VLANs : 20 DMZ Unrestricted
Dual ISPs : Enabled perpetual
VLAN Trunk Ports : 8 perpetual
Inside Hosts : Unlimited perpetual
Failover : Active/Standby perpetual
Encryption-DES : Enabled perpetual
Encryption-3DES-AES : Enabled perpetual
AnyConnect Premium Peers : 2 perpetual
AnyConnect Essentials : Disabled perpetual
Other VPN Peers : 25 perpetual
Total VPN Peers : 25 perpetual
Shared License : Disabled perpetual
AnyConnect for Mobile : Disabled perpetual
AnyConnect for Cisco VPN Phone : Disabled perpetual
Advanced Endpoint Assessment : Disabled perpetual
UC Phone Proxy Sessions : 2 perpetual
Total UC Proxy Sessions : 2 perpetual
Botnet Traffic Filter : Disabled perpetual
Intercompany Media Engine : Disabled perpetual
Cluster : Disabled perpetual
This platform has an ASA 5505 Security Plus license.
Serial Number: JMX01234567
Running Permanent Activation Key: 0x01234567 0x01234567 0x01234567 0x01234567 0x01234567
Configuration register is 0x1
Configuration has not been modified since last system restart.
FW1#
After analyzing the output provided above, you can see that this ASA is running 9.1(1) and has a Security Plus license supporting 20 VLAN’s, Dual ISP’s, Unlimited Inside Hosts and Failover.
Objective 2. – Users have been complaining about performance when accessing the internet. Determine the memory and processor utilization on your firewall.
FW1# show memory Free memory: 277952560 bytes (52%) Used memory: 258918352 bytes (48%) ------------- ------------------ Total memory: 536870912 bytes (100%) FW1# FW1# show cpu CPU utilization for 5 seconds = 10%; 1 minute: 7%; 5 minutes: 7% FW1#
