Configuring Cisco ASA NAT Pooling
Dynamic NAT Pooling, also known as NAT Pooling is a method of dynamically assigning real IP addresses to a dedicated mapped IP Address. In this lab you’ll learn how to configure and verify NAT Pooling along with PAT fallback on the Cisco ASA running 9.x
- Core Knowledge
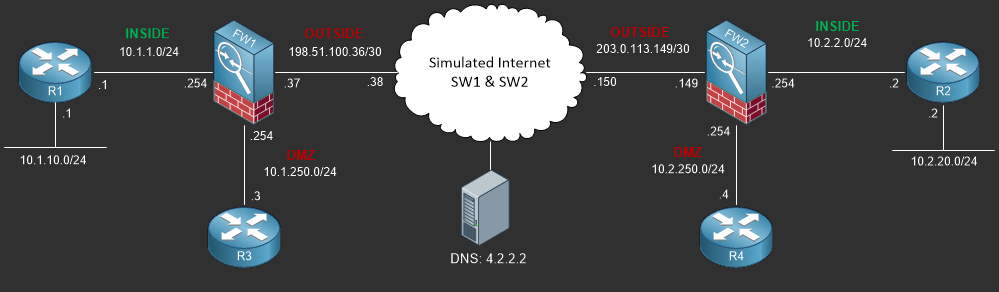
- Lab Topology
- Initial Configs
- Lab Objectives
- Lab Instruction
Core Knowledge and Real World Scenarios
One of the more uncommon NAT scenarios you may or may not encounter is NAT Pooling. This type of NAT is relatively simple in that instead of using PAT to translate Many IP Addresses to a single IP ADdress, NAT Pooling takes INSIDE Addresses and translates them to a pool of IP Addresses on the egress interface on a first come first serve basis.
For example, you have 20 machines inside your company and you have 30 public IP Addresses. If you had the need you could create a NAT Pool so that every workstation in the company would effectively have its own public IP Address. This is uncommon and often times very wasteful of IP Addresses unless there is an absolute need for this type of architecture.
In the past, one of the most common places you would have encounter this type of deployment is college dormitories where each student has their own public IP Address. Now days Colleges and Universities use software along with identity services to make sure the individual accessing the internet is indeed a student. This software allowed IP to Student tracking along with policy enforcement such as student PC’s must had Anti-Virus installed, all updates, etc… prior to being authorized to access the internet. Think back to all the years the RIAA sued students for downloading illegal music on college campuses, this is how a name was associated to the IP Address. One common software deployment is Cisco ISE (Identity Services Engine). If you’re interested in this type of technology we recommend that you peruse the Cisco CCNP Security, specifically the 300-208 Exam.
NAT Pooling can still be encountered today in small service provider networks and dormitories around the world however you’ll very rarely encounter it in the wild as newer technologies have replaced the functionality of NAT pooling with more intelligence such as identity based NAT which assigns the same public IP address to an internal machine based on the users identity via username/password or some other form of identification. (machine mac, certificate, token, etc..)
NAT Pooling is a relatively simple configuration, an example is provided below;
object network WAN_NAT_POOL range 203.0.113.21 203.0.113.13 object network INSIDE_NAT_POOL_HOSTS-10.2.20.0 subnet 10.2.20.0 255.255.255.0 nat (INSIDE,OUTSIDE) dynamic WAN_NAT_POOL
First you must define an object with the POOL of addresses using the range command which will become the mapped IP Addresses followed by an object defining the REAL ip addresses and the NAT Policy, in this case example we’re dynamically pooling nodes sourced from the 10.2.20.0/24 network to a range of IP addresses (203.0.113.11 through 203.0.113.20) on the OUTSIDE interface. Note that there may be more internal IP’s than available public pool IP’s and in which case it is a first come first serve and once the pool is depleted, the remaining internal devices will not have access to OUTSIDE resources. The default timeout for NAT Pooling is 3 hours and is based on an idle-timeout.
There is one way that this be fixed to ensure that once all the POOL IP addresses are used, internal machines are still able to access the OUTSIDE resources. Dynamic PAT can be introduced as provided in the following example;
object network WAN_NAT_POOL range 203.0.113.21 203.0.113.23 object network INSIDE_NAT_POOL_HOSTS-10.2.20.0 subnet 10.2.20.0 255.255.255.0 nat (INSIDE,OUTSIDE) dynamic WAN_NAT_POOL interface
As you can see the “interface” keyword was added onto the NAT policy which basically tells the firewall after all pool IP addresses are depleted, PAT the following traffic to the OUTSIDE interface IP Address.
You can verify which internal REAL IP addresses are associated to which MAPPED IP Addresses using the show xlate command.
Commands You Should Know
As a network engineer implementing the technologies outlined in this lab you should be familiar with the following commands provided in the table below;
| Command | Description |
|---|---|
| nat (INSIDE,OUTSIDE) dynamic WAN_NAT_POOL interface | Dynamic NAT Pooling Policy defined in the the object configuration mapping the real IP address referenced by the object to a pool of mapped IP Addresses refereed by another object with PAT Fallback as referenced using the interface suffix. |
Lab Device Initial Configuration(s)
In Section 7 you’ll only be configuring FW1. You will however use other lab devices to verify your configuration on FW1.
If you completed the previous lab you can continue where you left off otherwise you’ll need to load the following initial configurations into their respective device(s);
Section 7 Pre-Configured Lab Device(s)
The following lab devices have been pre-configured to save you time as you’ll only be working with FW1 in Section 7.
In order to complete the labs in section 7 you MUST load the following pre-configuration(s);
Before you Start
This lab requires that you have access to a Cisco ASA. You can complete this lab using a virtual Cisco ASA within GNS3 or you can reserve free lab time on the Stub Lab to have access to a pair of Cisco ASA 5510 Series Firewalls which can be used to complete this lab.
Lab Objectives
In this lab you will complete the following objectives.
- Define an object to be used for NAT Pooling on FW1 using the 198.51.100.21 through 198.51.100.23 IP Range.
- Define an object referencing the internal network 10.1.10.0/24
- Configure a NAT Pooling Policy for the newly created internal network object to use the IP Addresses referenced in the object created in objective 1 and enable PAT fallback
- Verify your NAT Pooling configuration by pining 4.2.2.2 from R1 sourced from 10.1.10.11, 10.1.10.12, 10.1.10.13 and 10.1.10.14
- Verify that the NAT Pooling policy is correctly operating by viewing the translations table on FW1
One More Thing…
It is recommended that you attempt to complete these lab objectives the first time without looking at the Lab Instruction section.
If you are a student preparing for the Cisco CCNA Security Certification Exam than you are more likely to remember how to complete these objectives if you attempt to complete them the first time on your own with the use of the core knowledge section found in this lab. You should only resort to the Lab Instruction section to verify your work.
Lab Instruction
Objective 1. – Define an object to be used for NAT Pooling on FW1 using the 198.51.100.21 through 198.51.100.23 IP Range.
FW1# config terminal FW1(config)# object network FW1_WAN_NAT_POOL_ADDRESSES FW1(config-network-object)# range 198.51.100.21 198.51.100.23
Objective 2. – Define an object referencing the internal network 10.1.10.0/24
FW1(config-network-object)# object network R1_INTERNAL_NETWORK FW1(config-network-object)# subnet 10.1.10.0 255.255.255.0
Objective 3. – Configure a NAT Pooling Policy for the newly created internal network object to use the IP Addresses referenced in the object created in objective 1 and enable PAT fallback.
FW1(config-network-object)# nat (INSIDE,OUTSIDE) dynamic FW1_WAN_NAT_POOL_ADDRESSES interface
Objective 4. – Verify your NAT Pooling configuration by pining 4.2.2.2 from R1 sourced from 10.1.10.11, 10.1.10.12, 10.1.10.13 and 10.1.10.14
R1#ping 4.2.2.2 source 10.1.10.11 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 4.2.2.2, timeout is 2 seconds: Packet sent with a source address of 10.1.10.11 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/2/4 ms R1#ping 4.2.2.2 source 10.1.10.12 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 4.2.2.2, timeout is 2 seconds: Packet sent with a source address of 10.1.10.12 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/4/12 ms R1#ping 4.2.2.2 source 10.1.10.13 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 4.2.2.2, timeout is 2 seconds: Packet sent with a source address of 10.1.10.13 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/2/4 ms R1#ping 4.2.2.2 source 10.1.10.14 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 4.2.2.2, timeout is 2 seconds: Packet sent with a source address of 10.1.10.14 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/3/4 ms R1#
Objective 5. – Verify that the NAT Pooling policy is correctly operating by viewing the translations table on FW1
FW1# show xlate
8 in use, 8 most used
Flags: D - DNS, e - extended, I - identity, i - dynamic, r - portmap,
s - static, T - twice, N - net-to-net
NAT from OUTSIDE:0.0.0.0/0 to INSIDE:0.0.0.0/0
flags sIT idle 1:01:05 timeout 0:00:00
NAT from DMZ:10.1.250.11 to OUTSIDE:198.51.100.11
flags s idle 1:02:02 timeout 0:00:00
TCP PAT from DMZ:10.1.250.12 80-80 to OUTSIDE:198.51.100.12 8080-8080
flags sr idle 1:02:02 timeout 0:00:00
TCP PAT from DMZ:10.1.250.13 80-80 to OUTSIDE:198.51.100.37 80-80
flags sr idle 1:02:01 timeout 0:00:00
NAT from INSIDE:10.1.10.11 to OUTSIDE:198.51.100.23 flags i idle 0:01:05 timeout 3:00:00
NAT from INSIDE:10.1.10.12 to OUTSIDE:198.51.100.21 flags i idle 0:01:01 timeout 3:00:00
NAT from INSIDE:10.1.10.13 to OUTSIDE:198.51.100.22 flags i idle 0:01:00 timeout 3:00:00
ICMP PAT from INSIDE:10.1.10.14/7 to OUTSIDE:198.51.100.37/7 flags ri idle 0:00:00 timeout 0:00:30
FW1#