Preventing IP Spoofs using IP Source guard
Prevent forged IP packets from attackers who conceal their identity by impersonating other computer systems on the network by using IP Source guard.
- Core Knowledge
- Lab Topology
- Initial Configs
- Lab Objectives
- Lab Instruction
Core Knowledge and Real World Scenarios
IP Address Spoofing is actually a common type of attack when attempting to gather information from unsecured networks. IP Source Guard is a technology that uses the DHCP Snooping database to identify spoofed IP packets based on inconsistent IP/MAC Bindings. If an IP address sends traffic from a MAC address that does not match in the DHCP Snooping database then the switch knows that the sender of that frame is trying to use the IP Address allocated to someone else and blocks the traffic at the layer 2 port.
IP Source Guard in a nut shell is a switch mechanism to block traffic from sources impersonating legitimate host(s) on the network.
You would never want to communicate with someone who aren’t who they say they are so why would you not want to take the same precautions on a computer network?
IP Source Guard is easily configured in one of two ways. The first being that you simply enable it on a layer 2 by executing the ip verify source command in interface configuration mode or by manually creating a ip source binding by using the ip source binding 0011.0011.0011 vlan 5 10.1.1.11 interface FastEthernet0/5 command in global configuration.
You can however enable IP source guard to verify the MAC address as well to prevent MAC address spoofing by using ip verify source port-security command in interface configuration mode. This however requires port-security and dhcp snooping to function properly.
To view ip source bindings, you’ll use the show ip source binding in privileged mode.
Familiarize yourself with the list of command(s) compiled below;
| Command | Description |
|---|---|
| ip verify source | This command when executed in interface configuration mode enables ip source guard and verify’s all incoming IP packets with the DHCP Snooping database |
| ip verify source port-security | This command when executed in interface configuration mode enables IP Source Guard verifying ip packets and mac addresses based on dhcp snooping db and port security. |
| ip source binding 0011.0011.0011 vlan 5 10.1.1.11 interface FastEthernet0/5 | This command when executed in global configuration creates a manual ip source guard binding specifying the MAC, Vlan and IP Address bound to a specific interface. |
| show ip source binding | This command when executed in priviledged mode displays all ip source guard binding information. |
To get started with this lab exercise please review the lab topology and prerequisites prior to loading initial configs and attempting the objective(s).
Lab Logical Topology
The following logical topology is used in all labs found through out Section 1 of the CCNA Security Workbook;
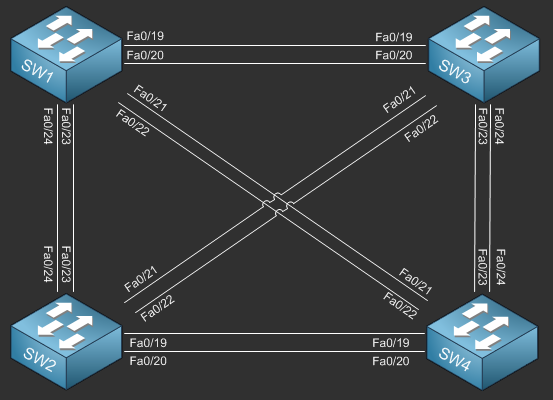
To view the physical cabling topology please visit the Topology page.
Lab Device Initial Configurations
Before you Start
This lab requires that you have access to a real Cisco Catalyst Series Switches. You cannot complete this lab using a NM-16ESW in GNS3. If you do not have a Cisco Catalyst Switch you can reserve free lab time on the Stub Lab to have access to four Cisco Catalyst 3560 Series switches which can be used to complete this lab.
If you completed the previous lab you can continue where you left off otherwise you will need to load the initial configurations provided in the previous tab to complete this lab.
Lab Objectives
In this lab you will complete the following objectives.
- On SW1 enable IP Source Guard on FastEthernet0/1 to verify IP packets and MAC frames.
- Verify your configurations by viewing the source guard binding table.
One More Thing…
It is recommended that you attempt to complete these lab objectives the first time without looking at the Lab Instruction section.
If you are a student preparing for the Cisco CCNA Security Certification Exam than you are more likely to remember how to complete these objectives if you attempt to complete them the first time on your own with the use of the core knowledge section found in this lab. You should only resort to the Lab Instruction section to verify your work.
Lab Instruction
Objective 1. – On SW1 enable IP Source Guard on FastEthernet0/1 to verify IP packets and MAC frames.
SW1>enable SW1#config t Enter configuration commands, one per line. End with CNTL/Z. SW1(config)#interface fa0/1 SW1(config-if)#ip verify source port-security SW1(config-if)#end SW1#
Objective 2. – Verify your configurations by viewing the source guard binding table.
SW1#show ip source bindings
MacAddress IpAddress Lease(sec) Type VLAN Interface
------------------ --------------- ---------- ------------- ---- --------------------
00:23:5E:01:F7:E8 10.1.1.2 84074 dhcp-snooping 1 FastEthernet0/1
Total number of bindings: 1
SW1##
