Preventing Layer 2 Loops with BPDU Guard
Most engineers do not take layer 2 loops as seriously as they should. Don’t get caught behind the curve when it comes to preventing accidental or intentional layer 2 loops in your network by not implementing BPDU Guard.
- Core Knowledge
- Lab Topology
- Initial Configs
- Lab Objectives
- Lab Instruction
Core Knowledge and Real World Scenarios
How much money would your company lose if your network had a 15 second outage? For anyone in the retail or transactional business this could equate to millions.
One of the biggest security threats to any network not because of an intrusion but because of an outage is from layer 2 spanning-tree loops. A single broadcast storm can cripple a 10Gigabit network in a matter of seconds.
Sometimes network engineers fight with enabling BPDU Guard due to the nature of its operation. It disables the port when someone plugs in an unauthorized switch to the network on the configured port. This configuration can be very frustrating in some environments where users want to add another device in their office so they just plug in a small consumer grade switch and magically their network drop in their office quits working.
If this individual happens to be an executive or a person of high respect in the office then their complaints could result in disabling BPDU Guard globally on the network which could indirectly lead to a network outage down the road due to their misunderstanding of the technology and the need to have such security precautions in place to prevent such a devastating outage.
Most network outages from broadcast storms happen from misconfiguration or accidental looping in the network. For example someone plugs in a small switch in their office and they plug both jacks in their office into this switch because they assume they’ll get double the bandwidth but a misconfiguration could possibly result in a short outage if the switch does not pass BPDU’s.
The majority of these types of problems are caused unintentionally however in the hands of the right perpetrator, this type of attack could cripple a network in a matter of seconds.
BPDU Guard is simplistic in nature and when configured on an interface it will shutdown the interface if a BPDU Guard is received on that interface. Any interfaces that are shutdown by BPDU Guard will show (ERR-Disabled) as their interface status.
You can enable BPDU Guard on a per interface basis using the spanning-tree bpduguard enable or globally on all access ports using the spanning-tree portfast bpduguard default which will also enable portfast on all access ports as well.
One key thing to keep in mind is that BPDU Guard may problems in enterprise environments such as an increase in helpdesk tickets however you can configure the switch to automatically recover the ERR-Disabled port by configuring errdisable recovery in global configuration mode using the errdisable recovery interval 300 and errdisable recovery cause bpduguard commands. This will automatically recover the shutdown interface caused by bpduguard in 300 seconds (5 minutes).
It is highly recommended in modern networks that portfast and BPDU Guard be enabled on edge access ports to ensure STP transitions the port to forwarding immediately and disables the port if ANY ingress BPDU’s are received on edge access ports.
Familiarize yourself with the list of command(s) compiled below;
| Command | Description |
|---|---|
| spanning-tree bpduguard enable | This command when executed in interface configuration mode enables BPDU Guard on the respective interface. |
| spanning-tree portfast bpduguard default | This command when executed in global configuration mode enables portfast and BPDU Guard on all access ports. |
| errdisable recovery interval 300 | This command when executed in global configuration mode will set the errdisable recovery interval in seconds. |
| errdisable recovery cause bpduguard | This command when executed in global configuration mode will recover any bpduguard errdisabled interfaces in the configured interval period. |
To get started with this lab exercise please review the lab topology and prerequisites prior to loading initial configs and attempting the objective(s).
Lab Logical Topology
The following logical topology is used in all labs found through out Section 1 of the CCNA Security Workbook;
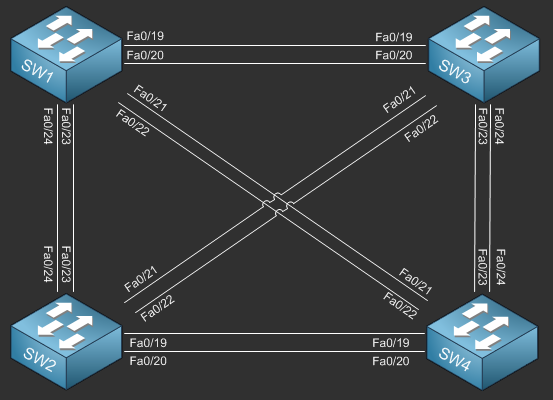
To view the physical cabling topology please visit the Topology page.
Lab Device Initial Configurations
The following initial configurations are provided as a base configuration to start the lab with. You may copy and paste these configurations directly into the terminal window of Stub Lab devices.
Before you Start
This lab requires real Cisco Switches. You can reserve lab time on the Stub Lab to have free access to Cisco Catalyst 3560 Series switches which can be used to complete this lab. To make things
easier you may load the initial configurations provided in this lab as a base config.
Please note that this lab cannot be performed in GNS3 using the NM-16ESW.
Lab Objectives
In this lab you will complete the following objectives.
- Configure FastEthernet0/1 on SW1 to shutdown the interface if BPDU’s are detected.
- On SW2, configure BPDU Guard on all access ports using a single command.
- Configure SW2 to automatically recover ERR-Disabled ports caused by BPDU Guard after 300 seconds.
One More Thing…
It is recommended that you attempt to complete these lab objectives the first time without looking at the Lab Instruction section.
If you are a student preparing for the Cisco CCNA Security Certification Exam than you are more likely to remember how to complete these objectives if you attempt to complete them the first time on your own with the use of the core knowledge section found in this lab. You should only resort to the Lab Instruction section to verify your work.
Lab Instruction
Objective 1. – Configure FastEthernet0/1 on SW1 to shutdown the interface if BPDU’s are detected.
SW1>enable SW1#config t Enter configuration commands, one per line. End with CNTL/Z. SW1(config)#interface fa0/1 SW1(config-if)#spanning-tree bpduguard enable SW1(config-if)#end SW1#
Objective 2. – On SW2, configure BPDU Guard on all access ports using a single command.
SW2>enable SW2#config term SW2(config)#spanning-tree portfast bpduguard default
Objective 3. – Configure SW2 to automatically recover ERR-Disabled ports caused by BPDU Guard after 300 seconds.
SW2(config)#errdisable recovery interval 300 SW2(config)#errdisable recovery cause bpduguard SW2(config)#end SW2#
